Jump To Section
- 1 Is speed still the real constraint in financial services engineering?
- 2 Control Techniques in Regulated Environments
- 3 How To Modernize Legacy Core without Losing Control
- 4 Composable architecture as a risk strategy
- 5 Greenfield vs. Brownfield: How Control Plays Differently
- 6 How does release engineering separate deployment from risk exposure?
- 7 Why observability replaces confidence in AI-enabled systems
- 8 What engineering leaders must explicitly own in 2026
- 9 Final Takeaway: How Much Change Can You Safely Absorb
- 10 FAQs
Financial institutions have spent the past decade accelerating delivery. CI/CD is in place. Automation is improving. AI is entering engineering workflows.
Yet many leadership teams still hesitate to release boldly, not because teams lack speed, but because institutions lack confidence that change can be contained once it reaches production.
Under increasing scrutiny from the OCC, FDIC, Federal Reserve, and state insurance regulators, the question has shifted:
It is no longer, “How fast can we ship?”
It is, “How safely can we absorb change?”
In this article, we reframe the engineering constraint in financial services, introducing a practical model of layered engineering control that helps financial institutions modernize legacy systems, adopt AI responsibly, and strengthen operational resilience without slowing innovation. The sections that follow address the core executive questions shaping engineering strategy in 2026.
Is speed still the real constraint in financial services engineering?
No. In many financial institutions, deployment speed has improved through automation and CI/CD. However, even when teams can deploy frequently, organizations may still experience “release hesitation”, not because teams are slow, but because leaders aren’t confident that outcomes remain controllable after release.
That concern is consistent with broader governance and risk thinking: mature organizations tend to strengthen risk appetite, stress testing, and oversight mechanisms as complexity rises, particularly in highly regulated industries like financial services.
Today, the biggest constraint is no longer how fast code moves through the pipeline; it is whether changes are contained, observable, reversible, and auditable once they reach production, especially under OCC, FDIC, Federal Reserve, and NAIC scrutiny, and amid growing third-party and AI risk.
This shift is likely to accelerate as institutions adopt AI across customer engagement, operations, fraud, risk, and engineering workflows, introducing new failure modes that are harder to predict and harder to audit. In this environment, competitive advantage can move from “how fast we ship” to “how reliably we can control how it is contained, governed, and reversed after release”.
Control Techniques in Regulated Environments
Control in regulated enviorments means designing systems so changes are isolated, observable, reversible, and auditable by default. It shifts governance from manual approvals to embedded technical mechanisms inside pipelines and runtime systems.
In 2026-style financial engineering, “control” is not just synonymous with compliance sign-offs but acts as a delivery and runtime mechanism that keeps systems safe under real-world variability.
Types of controls include:
A) eWalls (boundary controls)
These are “walls” that prevent unintended spread:
- network segmentation / micro-segmentation
- isolation between domains (identity, payments, fraud)
- strict service-to-service permissions
- separation of duties for sensitive operations
This logic is aligned with modern regulatory expectations around operational resilience and ICT/third-party risk management: resilience is increasingly about containment, monitoring, and governance of critical services.
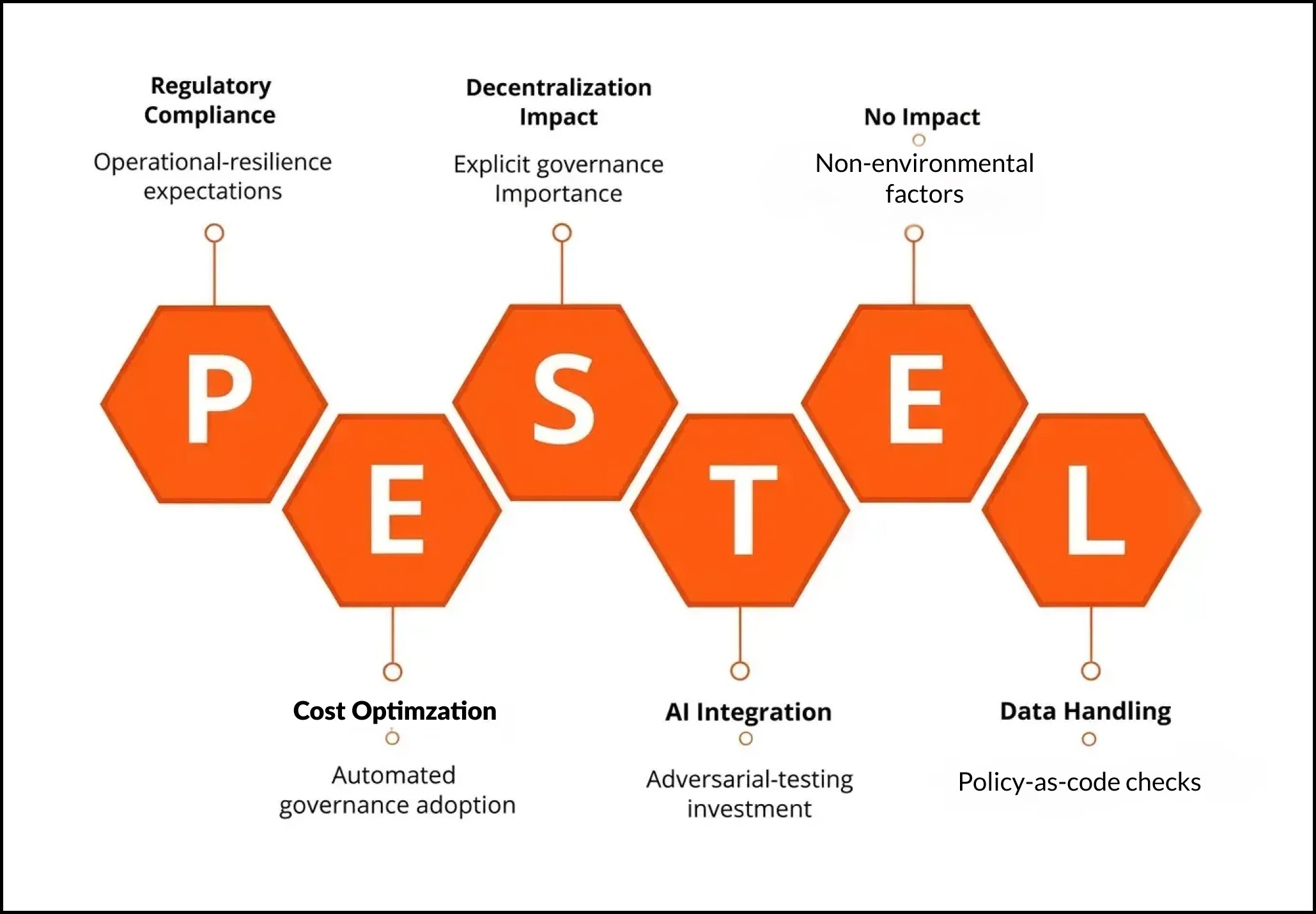
B) Release process controls
Release controls may evolve from “manual approvals” to automated governance:
- policy-as-code checks (security, privacy, logging, data handling)
- auditable gates
- standardized rollback criteria
- release playbooks that are rehearsed, not aspirational
Research also shows DevOps teams can struggle to demonstrate control to auditors due to decentralization and automation, making explicit governance frameworks and evidence trails more important over time.
Below is a PESTLE analysis of these controls:
C) Pipeline & workflow controls
This is where control becomes systemic:
- CI/CD guardrails (SAST/DAST, dependency scanning, secret scanning)
- provenance/attestation for builds
- environment promotion rules
- automated change records and traceability
Controls that rely on “people remembering steps” may fade; controls embedded in pipelines may dominate because they produce consistent evidence.
D) Red teaming (and resilience testing)
As systems become more complex (and AI-enabled), teams may invest more in:
- adversarial testing (prompt/abuse scenarios where AI exists)
- security red teaming
- chaos experiments to validate containment assumptions
The evolution from manual sign-offs to embedded governance reflects a broader DevOps governance tension described in academic and industry research. Automation improves speed but can complicate auditability unless evidence is deliberately engineered.
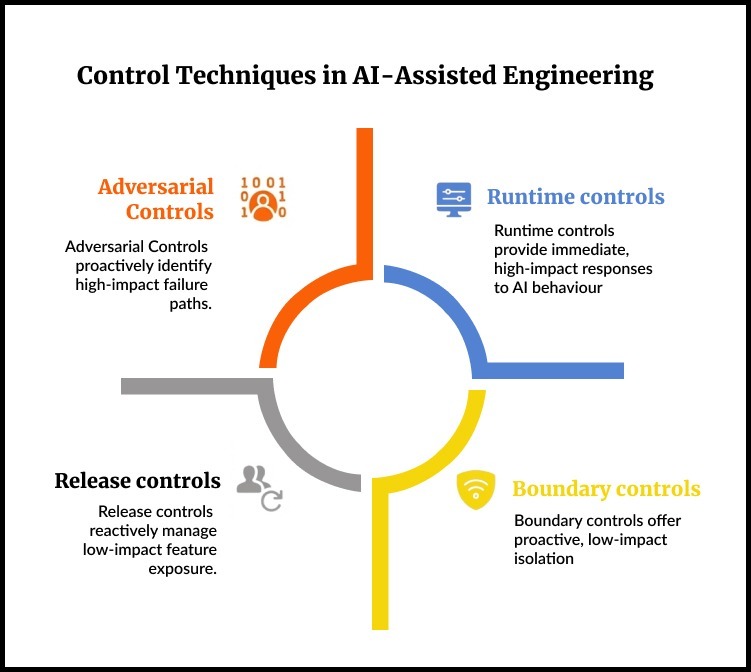
So, to sum, the four techniques of control include:
- Boundary controls (eWalls)
Isolation, segregation, and least privilege to reduce blast radius.
- Release controls (progressive + reversible delivery)
Feature flags, canary releases, kill switches, gradual exposure.
- Adversarial controls (red teaming + resilience tests)
Proactively discover failure paths before customers and regulators do.
- Runtime controls (observability + response automation)
Continuous monitoring and decision-quality visibility, especially for AI behavior.
How To Modernize Legacy Core without Losing Control
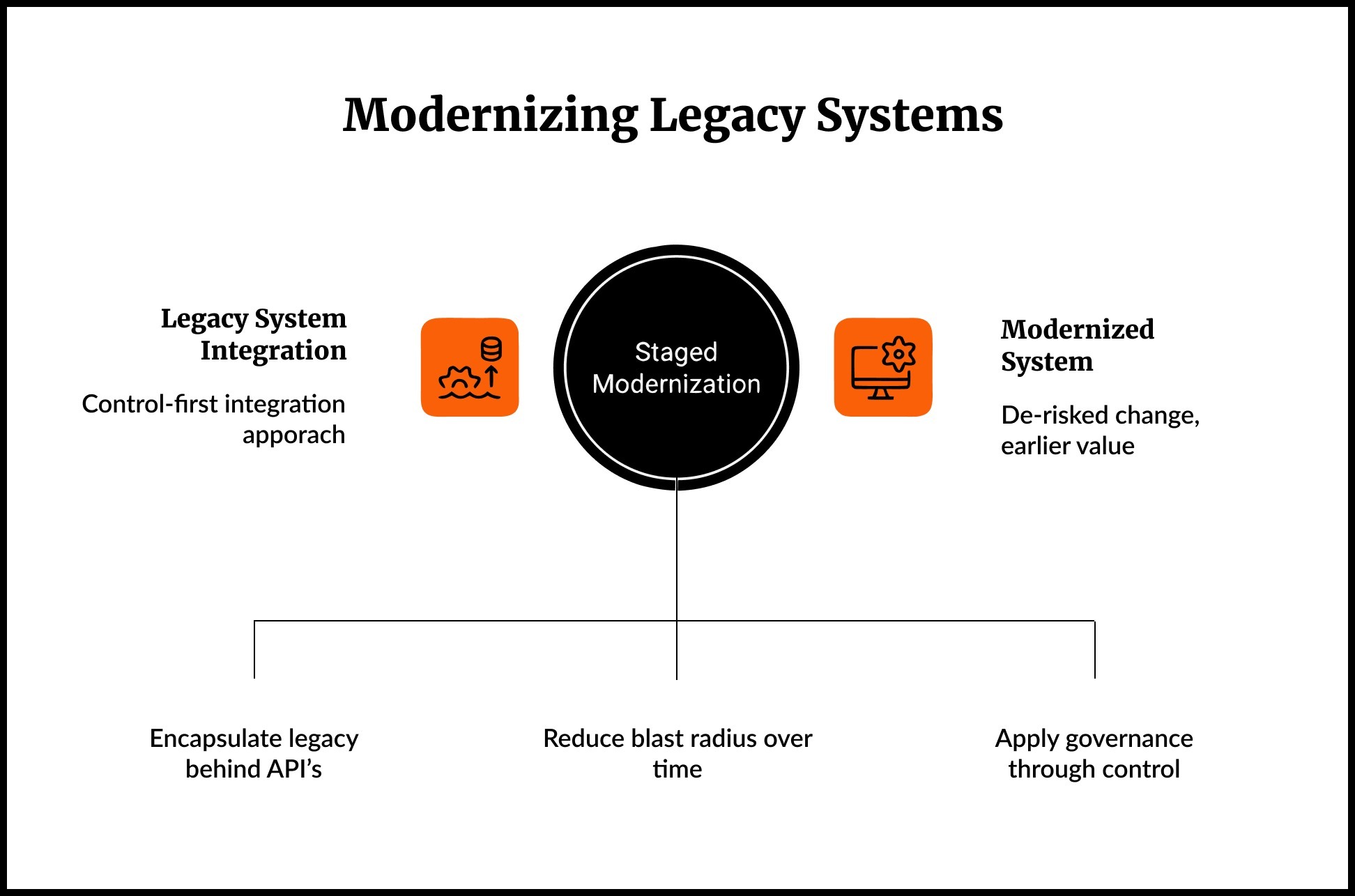
Financial services will likely remain a hybrid world: modern services + legacy cores.
The control risk is real: modernization can accidentally create visibility gaps (no telemetry), governance gaps (no traceability), and release gaps (core change windows still drive everything).
The most effective controls reduce blast radius through isolation, progressive release, adversarial testing, and continuous runtime visibility, not through slower deployment.
A practical control model for financial institutions should be structured as follows:
Pattern 1: “Wrap and govern” (control-first integration)
- encapsulate legacy behind well-defined APIs
- enforce access controls, throttling, and auditing at the boundary
- inject observability at the edge (tracing, structured logs, golden signals)
Pattern 2: Progressive decomposition (reduce blast radius over time)
Instead of a big-bang core replacement, many banks may prefer staged modernization. Bain has described staged transformation approaches and highlights how traditional core replacements can take years, pushing institutions toward strategies that deliver value earlier while de-risking change.
Pattern 3: Control surfaces (where governance “lives”)
If legacy cannot change quickly, control can still be applied through:
- API gateway governance
- release orchestration layer
- centralized policy enforcement
- telemetry pipelines and incident workflows
Deloitte also notes modernization pressure driven by shrinking legacy talent pools, making it more urgent to evolve, even if full replacement is unrealistic.
Composable architecture as a risk strategy
Composable architecture may be framed as agility but in financial services it can function as risk containment:
- decouple high-risk change areas from core systems
- isolate AI-enabled components behind stable contracts
- constrain blast radius by domain boundaries
- replace modules without full-system regression risk
It has consistently pushed “composable” thinking across industries; third-party summaries and ecosystem discussions also emphasize low composability maturity in financial services.
The control advantage becomes strategic: composability can turn modernization into a series of bounded-risk moves rather than one existential migration.
For a true competitive advantage in 2026, keep up with these Trends Shaping How Financial Institutions Modernize with AI-Assisted Engineering.
Greenfield vs. Brownfield: How Control Plays Differently
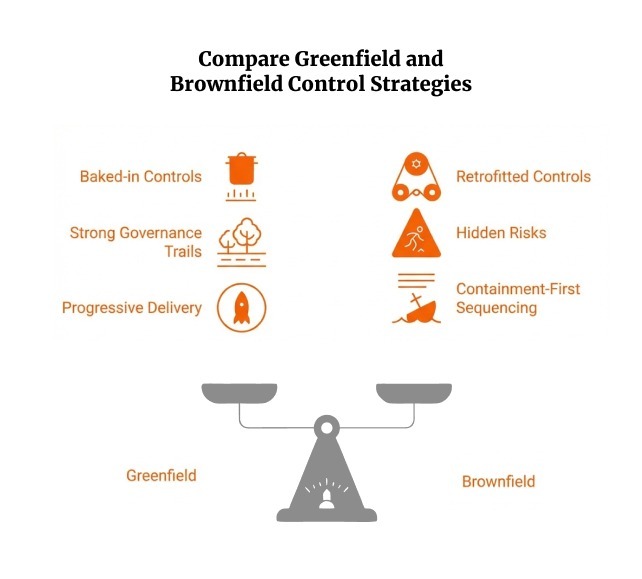
Control plays differently in greenfield and brownfield environments. Greenfield programs allow governance to be designed in from the start, while brownfield modernization requires retrofitting containment around legacy complexity. In mid-market financial institutions, brownfield control strategy is often the higher-stakes challenge.
Greenfield: Control by Design
In greenfield initiatives (new digital banks, new product lines, AI-native platforms) engineering teams can embed control mechanisms from day one:
- Policy-as-code in CI/CD
- Observability-by-default
- Progressive delivery and feature gating
- Explicit service boundaries
- Automated evidence trails
This environment allows institutions to align technical architecture with regulatory expectations around auditability and resilience from the beginning.
However, greenfield introduces a different control risk: third-party dependency concentration. Many greenfield builds rely heavily on cloud providers, fintech vendors, and managed services. For mid-market institutions, this can increase exposure to vendor risk and reduce internal visibility into critical components.
Greenfield is structurally cleaner but often externally dependent.
Brownfield: Control by Containment
Brownfield environments are more common in mid-market banks and insurers. Core platforms may be decades old. Business logic may be undocumented. Change windows may still be batch-driven.
Here, control cannot be assumed; it must be imposed.
Key risks include:
- Hidden coupling across systems
- Limited telemetry
- Manual change evidence
- Knowledge concentrated in shrinking legacy talent pools
Industry commentary, including Deloitte’s work on legacy modernization in banking (2023), highlights workforce and operational pressure as a driver of modernization urgency.
The practical control strategy in brownfield contexts is containment-first:
- Wrap legacy systems behind governed APIs
- Inject observability at integration edges
- Segment high-risk domains
- Gradually extract functionality
Brownfield control is not about rebuilding everything. It is about reducing blast radius before accelerating change.
How does release engineering separate deployment from risk exposure?
Release engineering reduces risk exposure by allowing code to be deployed without immediately exposing behavior to all users.
This distinction matters in regulated environments.
As complexity rises, strong teams may separate:
- deploying code from
- releasing behavior
Feature flags and progressive delivery let institutions:
- release to limited segments
- instantly turn off risky capabilities
- reduce incident impact without full rollbacks
This is the practical embodiment of “control beats speed.”
For institutions under scrutiny for change management discipline, release engineering becomes a visible demonstration of engineered control.
Why observability replaces confidence in AI-enabled systems
Traditional confidence came from pre-production testing. In complex, distributed, and AI-influenced systems, confidence may shift to continuous verification in production.
In our experience, observability framing emphasizes enriching telemetry with context (dependencies + business service relationships), which aligns with “control as a live system,” not a one-time audit artifact.
For banks and insurers, this means:
- AI behavior must be observable at runtime
- Telemetry must connect technical events to business services
- Governance must extend beyond static validation
Confidence shifts from “we tested it” to “we are continuously verifying it.”
What engineering leaders must explicitly own in 2026
Engineering leadership in financial services must increasingly own:
- Control architecture (where isolation, governance, and reversibility are designed-in)
- Evidence trails (auditable delivery + runtime traceability)
- AI governance integration with model risk management expectations
Practical model risk governance guidance for GenAI in financial services is emerging from reputable institutions (e.g., Alan Turing Institute) and aligns with adapting established MRM frameworks for GenAI.
- Operational resilience posture (containment, monitoring, third-party dependencies)
Regulators increasingly expect demonstrable control over critical services and vendor ecosystems. Vendor concentration risk, in particular, introduces systemic exposure if control mechanisms are not institutionally owned.
In this context, engineering leadership becomes accountable not only for building systems but for defining the institution’s technical risk posture.
Final Takeaway: How Much Change Can You Safely Absorb
Financial institutions are not constrained by their ability to build. They are constrained by their ability to absorb change without destabilizing critical services.
Regulators are not asking how quickly you deploy but whether you can contain incidents, demonstrate traceability, manage third-party exposure, and govern AI-influenced systems with discipline. Boards are asking similar questions in different language: What is our real risk posture?
The institutions that move confidently in 2026 will not be those that ship the fastest. They will be those that have engineered control into their architecture, delivery systems, and runtime environments.
Control is not the opposite of speed. It is what makes sustainable speed possible.
The way forward looks like this: refine where isolation lives, how reversibility is guaranteed, how evidence is generated, and how observability informs governance. When those foundations are explicit, innovation becomes expandable rather than fragile.
FAQs
1. How do we modernize legacy core systems without increasing regulatory risk?
Modernization increases exposure if visibility, traceability, and containment are not engineered in first. A containment-first approach – wrapping legacy cores behind governed APIs, injecting observability at integration boundaries, segmenting high-risk domains, and progressively decomposing functionality – reduces blast radius before accelerating change. This allows institutions to modernize in stages while maintaining auditability and operational resilience.
2. How can we prove to regulators that our CI/CD pipeline is actually controlled?
Speed alone does not demonstrate discipline. Regulators look for evidence of containment, traceability, and reversibility. Embedded controls such as policy-as-code checks, automated change records, auditable release gates, build provenance, and standardized rollback mechanisms generate consistent evidence trails. Control must live inside pipelines and runtime systems, not in manual approvals alone.
3. What does “containment” really mean in a banking technology environment?
Containment means limiting the blast radius of change. Practically, this includes network and domain segmentation, strict service-to-service permissions, progressive delivery (feature flags, canary releases), kill switches, and runtime monitoring tied to business services. If an incident occurs, it should be isolated, observable, and reversible without destabilizing critical systems.
4. Why is release engineering critical for regulatory compliance and operational resilience?
Release engineering separates code deployment from user exposure. In regulated environments, this distinction reduces operational risk. Techniques such as feature flags, progressive delivery, canary releases, and kill switches allow institutions to limit exposure, reverse behavior quickly, and reduce incident impact without full rollbacks. This demonstrates engineered change discipline to regulators and strengthens operational resilience under real-world variability.
5. How does AI adoption change engineering control requirements in financial institutions?
AI introduces new failure modes that are harder to predict and audit. As AI becomes embedded in customer engagement, fraud detection, risk modeling, and engineering workflows, control must extend into runtime observability and model governance. Institutions must make AI behavior observable, connect telemetry to business services, and align delivery pipelines with model risk management expectations. Confidence shifts from pre-production testing to continuous verification in production.



